Dumping NTDS.DIT File from Active Directory
In recent pentest engagement we came across scenario where we need to download the password hashes of all the users on the domain for offline cracking. But none of the automated tools were working or either flagged by Antivirus. So let's use the tools present on the AD box only.
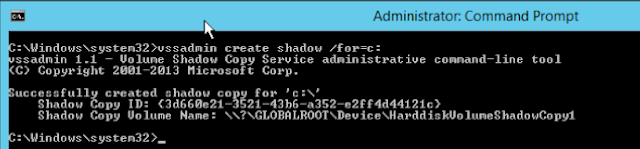
We need Administrator privileged command prompt on the AD, to perform below activity. First tool we use is called "vssadmin" which creates the shadow copy of the system drive.
In the above snippet the HarddiskVolumeShadowCopy1 means its the first Shadow copy of the C drive. Similarly there can be multiple copies created, do take the latest and freshly baked one.
Using the command :- vssadmin list shadows, we get list of the shadow copies created for insecure.com domain.
Alternatively there is a in-built command (Windows 2008 and later) named ntdsutil. It will create a snapshot of the Active Directory database along with copy of ntds.dit and SYSTEM file.
Sometimes ntds.dit appears to be corrupted, then we can use the built-in command-line tool Esentutl to repair same.
Esentutl /p c:\windows\ntds\ntds.dit
Successfully created (error free) ntds.dit file can be validated using DIT Snapshot Viewer.
Now copy these 3 files to Kali machine for further process. Download the below tools to aid us ahead.
Esedbexport (inside libesedb) is used to export database stored in an Extensible Storage Engine (ESE) Database (EDB) file. The exported data is stored in the ntds.export directory.
Then we use the Ntdsextract to extract the hashes from the exported data. Below are the necessary files from the ntds.export.
.....some more cropped data
If the domain is huge sometime's the size of NTDS.dit is in Gb's, in such scenario esedbexport takes alot time to parse the data. So here comes the secretdump.py (from Impacket) which just takes some seconds to parse ntds.dit file and get us output to feed to our favourite password cracking tool.
One more simple method to dump AD password hashes is using CrackMapExec. All the hashes are stored under /logs directory of crackmapexec.
Happy Cracking !!
We need Administrator privileged command prompt on the AD, to perform below activity. First tool we use is called "vssadmin" which creates the shadow copy of the system drive.
In the above snippet the HarddiskVolumeShadowCopy1 means its the first Shadow copy of the C drive. Similarly there can be multiple copies created, do take the latest and freshly baked one.
Using the command :- vssadmin list shadows, we get list of the shadow copies created for insecure.com domain.
- NTDS.dit
- SYSTEM
- SAM
Sometimes ntds.dit appears to be corrupted, then we can use the built-in command-line tool Esentutl to repair same.
Esentutl /p c:\windows\ntds\ntds.dit
Successfully created (error free) ntds.dit file can be validated using DIT Snapshot Viewer.
Now copy these 3 files to Kali machine for further process. Download the below tools to aid us ahead.
Esedbexport (inside libesedb) is used to export database stored in an Extensible Storage Engine (ESE) Database (EDB) file. The exported data is stored in the ntds.export directory.
Then we use the Ntdsextract to extract the hashes from the exported data. Below are the necessary files from the ntds.export.
- datatable
- link_table
.....some more cropped data
If the domain is huge sometime's the size of NTDS.dit is in Gb's, in such scenario esedbexport takes alot time to parse the data. So here comes the secretdump.py (from Impacket) which just takes some seconds to parse ntds.dit file and get us output to feed to our favourite password cracking tool.
One more simple method to dump AD password hashes is using CrackMapExec. All the hashes are stored under /logs directory of crackmapexec.
Happy Cracking !!










Thanks for sharing hacker ;)
ReplyDeleteAwesome blog
ReplyDeleteEconomists have proposed many theories about how humans make selections beneath completely different https://thekingofdealer.com/jumbo-casino/ threat conditions. Several of them can also be|may also be|can be} utilized to model gambling behaviors. For example, the prospect theory launched by Kahneman and Tversky4 and its variant cumulative prospect theory5 have been adopted in modeling on line casino gambling6.
ReplyDelete