Bypassing PaloAlto Traps EDR Solution
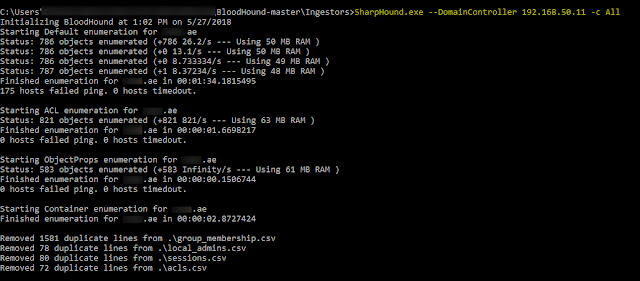
In recent Pentest we encountered PaloAlto Traps (EDR Solution) was installed on the compromised machine with WildFire module integrated in same. Challenge was to bypass same, since it was blocking and flagging lot many arsenal tools based on behavioral basis.
So the easiest solution came to mind is to disable using inbuilt utility i.e.; Cytool. Cytool is a command-line interface (CLI) that is integrated into Traps and enables you to query and manage both basic and advanced functions of Traps. Any changes you make using Cytool are active until Traps receives the next heartbeat communication from the Traps management service. On Windows endpoints, you can access Cytool using a Microsoft MS-DOS command prompt that you run as an administrator. Cytool is located in the C:\Program Files\Palo Alto Networks\Traps folder on the endpoint. We tried to disable service (Cyvrfsfd), but we failed due to supervisor password.
Then next was to try the trick Carlos shared in his Security Weekly podcast which talks about Filter Manager Control Program (fltMC.exe) binary and Altitude Numbers.
A file system filter driver (Minifilter) is an optional driver that adds value to or modifies the behavior of a file system. These filter drivers process all filesystem activity including background processes. Typical uses are: encryption software transparently encrypting new files. Enforcing file quotas and most commonly anti-virus software scanning file activity. Using fltMC.exe we can manage MiniFilter drivers (Load a Filter driver, Unload a Filter driver, etc)
Altitudes Number for Minifilter Drivers is number managed and alloted by Microsoft to different vendors depending on there requirements. For example, "FSFilter Anti-Virus" belongs to range 320000-329999 and "FSFilter Activity Monitor" belongs to 360000-389999, etc. You can also check the existing allotted Altitudes to different process by following this link (not updated after 2017 😑).
Only prerequisite is FLTMC requires an Elevated command prompt (either CMD or PowerShell). Lets try this trick in our scenario now and it worked like a charm by unloading Cyvrfsfd driver on Traps v4.1.4. Now you can run any offensive tools without any alerts/blocks.
Same trick also does work for Traps v5.0.3 (Altitude number -321234)
Note: - Above bypass (not a 0-day) would not work in some infrastructures, it all depends on how windows is configured and hardened. (If anybody knows the root cause of this, please do share with me)
Happy Hacking !!




Nice, fltmc will probably work anytime the inly thing important to notice is that you need admin access.
ReplyDeleteBtw what i like to do is to blacklist the fltmc executable using traps and by that deny the execution of it.
No need, you can just enabled the "Service Tampering" in the policy which will enable the "Child process Protection" module, and that is enough to protect against unloading the Cyvrfsfd via fltMC.
DeleteCool, but unfortunately this won't work if the Traps admin has enabled the "Child process Protection" module in the policy, in that case Traps will detect the unload command as malicious and stops it.
ReplyDeleteIn minifilter driver unload function, there are a flag that keep driver can not be unload manual. By checking this flag, deverloper can make driver can not be unload manual, or you aslo unset unload function pointer in DriverEntry object. The PaloAlto's deverlopers maybe forgot this tech :)
ReplyDeleteBy ThanhLN - Viettel EDR team from Vietnam
Could you show me this unload process? :) (flag that keep driver)
ReplyDeleteif Flags = FLTFL_FILTER_UNLOAD_MANDATORY just return STATUS_FLT_DO_NOT_DETACH
ReplyDeleteWhatsapp Number Call us Now! 01537587949
ReplyDeleteSEO Service in Bangladesh
USA pone web iphone repair USA
USA SEX WEB SEO Company in USA
bd sex video B tex
bd sex video sex video
bd sex video freelancing course