PrivExchange : One Hop away from Domain Admin
Recently we have been on Internal Network Pentest with end goal to demonstrate the compromising Domain Admin account or be one of them. As usual customer placed us in the User VLAN segregated from Admin VLAN. Then we started using Responder in order to gather some hashes or cleartext credentials over the wire. At end of the day, we got multiple hashes and cracked them using Hashcat to use them on next following day. But most of the cracked credentials belongs to users of Business, HR, Payrolls, etc (i.e.non-IT Staff 😕) and customer infrastructure was mostly Windows 10/2012/2016 mix and patched too.
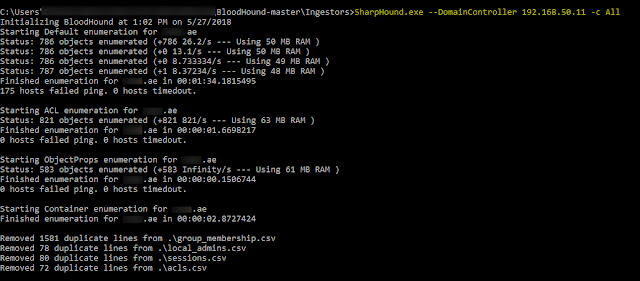
So we decided perform the privilege escalation in Microsoft Exchange setup i.e.; "PrivExchange" (Kudos to Dirk-jan for the attack). In our scenario we have compromised the user credentials and we would escalate the privileges of sample compromised user to perform DCSync attack.
So we decided perform the privilege escalation in Microsoft Exchange setup i.e.; "PrivExchange" (Kudos to Dirk-jan for the attack). In our scenario we have compromised the user credentials and we would escalate the privileges of sample compromised user to perform DCSync attack.
Required details to perform attack
Compromised username : victim-user (should have mailbox created)
Domain Controller : mydc02.pwnable.com
Exchange Server : myexch01.pwnable.com (192.168.100.200)
Attacker Machine IP : 192.168.10.100
Domain Name : pwnable.com
Git clone the PrivExchange and Impacket from Github.
Step-1: In this step we setup Ntlmrelayx in relay mode with target as Domain Controller and user to escalate.
Step-2: Here we use the Privexchange script along with our user and exchange server. Note: API Call response should be Successful
Step-3: After one minute we receive the connection back from Ntlmrelayx and which adds Replication-Get-Changes-All privileges to our supplied user.
Step-4: Now we perform the DCSync attack with our existing user
Reference :- https://blogs.technet.microsoft.com/exchange/2019/02/12/released-february-2019-quarterly-exchange-updates/
https://dirkjanm.io/abusing-exchange-one-api-call-away-from-domain-admin/
https://portal.msrc.microsoft.com/en-US/security-guidance/advisory/adv190007
https://github.com/gdedrouas/Exchange-AD-Privesc
Happy Hacking !!

Good and needy ways has been told well to keep a network more secure. A strong security culture not only interacts with the day-to-day procedures, but also defines how network security influences the things that your organisation provides to others.
ReplyDelete